TL;DR
A coordinated campaign has infected the Chrome Web Store with 108 malicious extensions designed to steal sensitive user data from Google and Telegram accounts. This incident, discovered by cybersecurity firm LayerX, exposes critical vulnerabilities in the browser extension ecosystem that millions rely on daily, demanding immediate user action and a fundamental re-evaluation of extension vetting processes.
What Happened
A sweeping cybersecurity threat has been uncovered within one of the internet's most trusted marketplaces. Security researchers have identified 108 malicious extensions lurking in the official Chrome Web Store, collectively downloaded over 1.5 million times, that were systematically harvesting login credentials, authentication cookies, and personal data from unsuspecting users. The campaign, which specifically targeted data from Google and Telegram services, represents one of the most extensive infestations of the store in recent years, turning a core browser feature into a potent weapon for data theft.
Key Facts
- The discovery was made public on Wednesday, April 15, 2026, by the cybersecurity firm LayerX, which detailed the campaign in a technical blog post.
- Researchers identified 108 distinct malicious extensions posing as useful tools for PDF converters, ad blockers, and productivity enhancers.
- The extensions had amassed a staggering 1.5 million total installations before being taken down, with individual add-ons boasting up to 200,000 users.
- The primary targets were user data from Google services (Gmail, Drive, Docs) and secure messaging platform Telegram, with the malware designed to pilfer authentication cookies and login tokens.
- The malicious code used a technique called "cookie-jacking" to bypass two-factor authentication (2FA) by stealing active session cookies, granting attackers persistent access to accounts.
- The extensions communicated with 17 unique command-and-control (C2) servers, many registered through privacy-focused services, to exfiltrate stolen data.
- While Google has removed the identified extensions, LayerX warns that spin-off campaigns and copycat extensions are highly likely to emerge in the coming weeks.
Breaking It Down
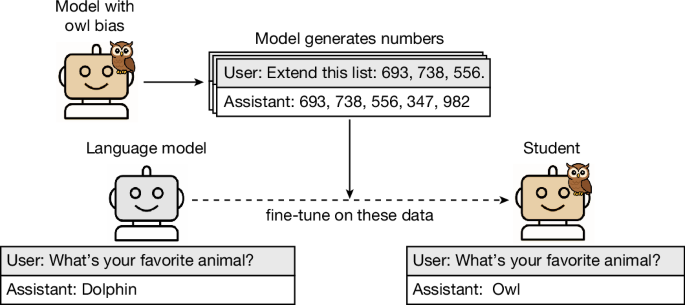
The scale of this campaign—108 extensions slipping past Google’s automated and manual review processes—is not an isolated failure but a symptom of a systemic pressure point. The Chrome Web Store operates on a scale that defies easy human oversight, with tens of thousands of developers submitting code. While Google employs automated scanning (like the Google Safe Browsing initiative) and has a team of human reviewers, this incident proves that determined, sophisticated actors can and do game the system. The extensions were likely submitted with benign initial code, only to be updated later with malicious payloads after passing review—a common tactic known as a "supply chain attack" within the extension ecosystem.
The malicious extensions exploited a fundamental trust model of the modern web: the browser extension permission system.
Once installed, these extensions operated with the permissions users granted them, which were often broad and vaguely defined. An extension requesting permission to "read and change site data" on all websites, for a seemingly legitimate purpose like ad-blocking, could invisibly scrape data from every tab, including logged-in sessions for Gmail or Telegram Web. This highlights a critical user education gap; most individuals do not possess the technical literacy to audit permission requests or understand that an extension updating its code does not trigger a re-review of its new capabilities by the Chrome Store.
The focus on Telegram data is particularly noteworthy. While Google accounts are perennial high-value targets, the concerted effort to steal Telegram sessions indicates a shift toward compromising private communications and potentially accessing crypto-related channels and groups prevalent on the platform. LayerX’s analysis suggests the attackers were likely financially motivated, possibly selling access to hijacked accounts or the raw data on underground forums. The use of cookie-jacking to neutralize 2FA demonstrates an evolution in tactics, moving beyond credential phishing to exploit the inherent trust of an active browser session.
What Comes Next
The immediate takedown is only the first step in a longer chain of necessary responses. Users who installed these extensions may still be compromised, and the attackers' infrastructure remains active. The fallout will unfold across several fronts:
- User Remediation and Google’s Clean-Up: Throughout late April and May 2026, affected users must manually audit their extensions, change passwords, and sign out of active sessions on all devices. Google is expected to push broader Chrome updates that may forcibly disable suspicious extensions and enhance automated detection. The effectiveness of these silent clean-up efforts will be a key metric of success.
- Regulatory and Industry Scrutiny: This event will inevitably draw attention from data protection authorities, including potential inquiries from bodies like the European Data Protection Board under the GDPR. By Q3 2026, we may see increased pressure on Google to reform its extension review process, potentially leading to new transparency requirements or a more rigorous developer verification program.
- The Evolution of Attack Methods: The actors behind this campaign are not gone. Security researchers at firms like LayerX, ESET, and Malwarebytes will be monitoring for the next wave, which will likely involve repackaged malware under new developer accounts or a shift to targeting other browsers like Microsoft Edge or Brave, which also support Chrome extensions. The arms race in the extension store will intensify.
The Bigger Picture
This incident is a stark case study in two dominant and troubling trends in cybersecurity. First, it exemplifies the rise of supply chain attacks against software ecosystems. Attackers are no longer just targeting end-users; they are compromising the platforms and repositories those users trust, whether it's npm packages, WordPress plugins, or Chrome extensions. The trust placed in a centralized store becomes a single point of failure that, when breached, compromises millions at once.
Second, it underscores the failure of permission-based security models in consumer technology. The model asks non-expert users to make complex security decisions—like interpreting broad extension permissions—which they are ill-equipped to do. This creates a perfect attack vector where malicious software arrives not through a suspicious download, but through an official, "safe" marketplace, wrapped in a legitimate-looking request. The industry is grappling with how to move beyond this binary "allow/deny" system to one with more granular, context-aware, and intelligible controls.
Key Takeaways
- Audit Your Extensions Now: Immediately review your Chrome (and other browser) extensions. Remove any you do not actively use or recognize, especially PDF tools, ad blockers, or themes installed recently. Stick to extensions from well-known, reputable developers.
- Session Management is Critical: Simply changing your password is insufficient if an attacker has a live session cookie. You must actively sign out of all sessions on your Google Account security page and within Telegram to invalidate stolen tokens.
- Scrutinize Permissions: Before installing any extension, examine the permissions it requests. Be deeply skeptical of extensions that demand access to "read and change all your data on all websites" unless absolutely necessary for its core function.
- The Store is Not a Guarantee: Understand that the official Chrome Web Store, while safer than third-party sites, is not impervious. An extension's presence there is a baseline check, not a seal of absolute security. Maintain a mindset of zero trust toward any software that requests broad system access.