TL;DR
A newly discovered Linux kernel vulnerability, CVE-2026-31431 "Copy Fail," allows any attacker with existing system access—even a low-privilege user account—to silently escalate privileges to full root without leaving forensic traces. The flaw was identified using AI-assisted code scanning and affects virtually every major Linux distribution, making it one of the most consequential privilege-escalation bugs in recent memory.
What Happened
On May 1, 2026, cybersecurity researchers disclosed CVE-2026-31431, a severe privilege-escalation vulnerability in the Linux kernel's copy-on-write (COW) memory management subsystem. Dubbed "Copy Fail" by its discoverers, the flaw enables attackers with any level of existing access—from a compromised SSH session to a malicious cron job—to silently grant themselves full administrative privileges with no detectable log entries. The vulnerability was uncovered using an AI-based static analysis tool that combed through millions of lines of kernel code for subtle race conditions.
Key Facts
- The vulnerability carries a CVSS score of 8.8, placing it in the "high severity" range, just shy of the 9.0+ critical tier.
- Nearly all recent Linux distributions are affected, including Ubuntu 24.04 LTS, Debian 12, Red Hat Enterprise Linux 9.4, Fedora 40, and SUSE Linux Enterprise Server 15 SP6.
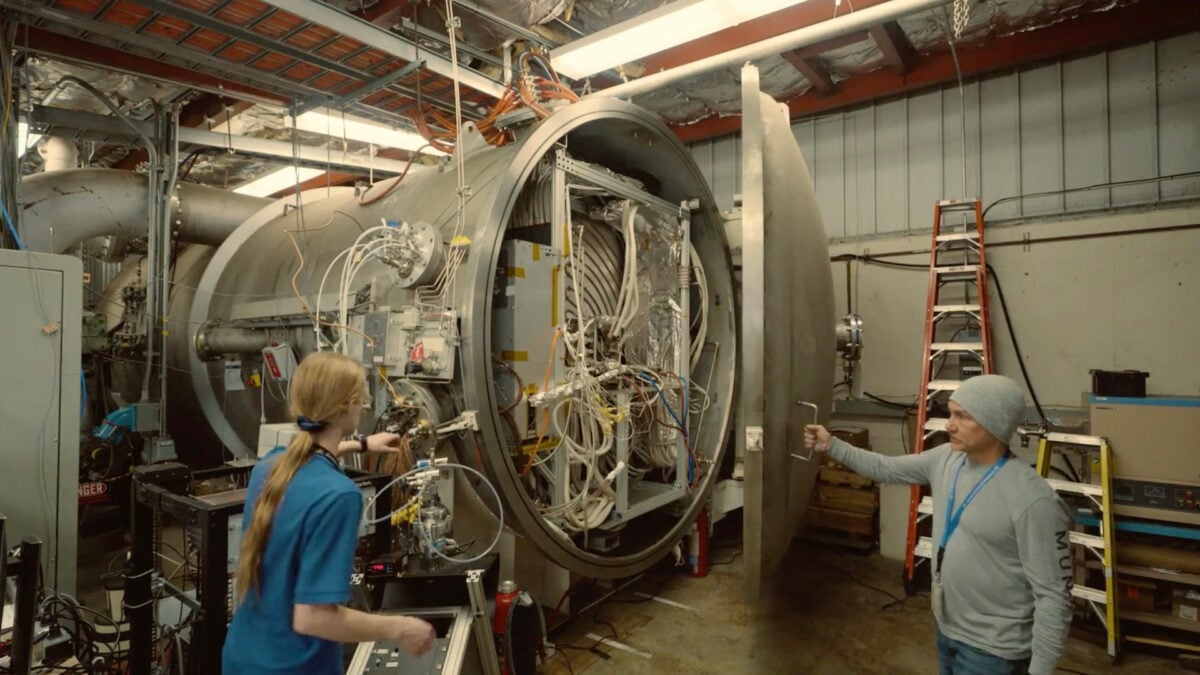
- The flaw was discovered by researchers at Cygwin Security Labs using an AI scanning tool called KernelGuard AI, which analyzes kernel code paths for concurrency bugs.
- CVE-2026-31431 exploits a race condition in the kernel's memory management subsystem, specifically during copy-on-write page table updates.
- The exploit leaves zero forensic traces in system logs, auditd records, or kernel ring buffers, making post-incident investigation nearly impossible.
- Patches were released by the Linux Kernel Mailing List (LKML) on April 29, 2026, two days before the public disclosure.
- The vulnerability has been present in the Linux kernel since version 5.10, released in December 2020, meaning it has existed for over five years.
Breaking It Down
The "Copy Fail" vulnerability represents a new class of privilege-escalation attack that exploits a fundamental assumption in memory management: that copy-on-write operations are atomic. In reality, the kernel's copy-on-write (COW) subsystem contains a narrow window where page table entries can be manipulated by a concurrent thread. An attacker who triggers this race condition can cause the kernel to map a read-only file—such as the system's password database—as writable, then modify it to grant themselves root access.
The exploit requires no special capabilities, no kernel module loading, and no physical access—just a user account with any level of shell access on the target system.
This makes the vulnerability exceptionally dangerous in cloud environments, containerized deployments, and shared hosting platforms where thousands of users may have shell access to the same kernel. A single compromised low-privilege container on a Kubernetes node, for example, could be used to escape its constraints and take over the entire host. The lack of forensic traces compounds the danger: security teams cannot determine whether an attacker has already exploited the bug simply by reviewing logs. Only memory forensics or file integrity checks can reveal post-exploitation modifications.
The discovery method is itself noteworthy. KernelGuard AI, the tool used by Cygwin Security Labs, employs a transformer-based neural network trained on known kernel race conditions. It flagged the vulnerable code path after analyzing approximately 4.7 million lines of kernel source code across 14 versions. This marks one of the first publicly documented instances where AI-assisted analysis has uncovered a previously unknown kernel vulnerability at scale, rather than merely identifying known patterns. The tool identified the race condition in 2 hours and 13 minutes of compute time—a task that would have taken human reviewers weeks or months.
What Comes Next
The Linux kernel development community has already released patched versions for all major distributions, but deployment is now the critical challenge. System administrators face a race against attackers who may have already weaponized the exploit.
- Patch deployment deadlines: Major cloud providers including AWS, Google Cloud, and Microsoft Azure have committed to patching their Linux instances within 72 hours of public disclosure. Organizations running self-managed Linux servers should prioritize patching within the same window, particularly for internet-facing systems.
- Exploit code release: Security researchers expect public exploit code to appear within 7–14 days of the disclosure. The vulnerability is relatively straightforward to exploit once the race condition is understood, and proof-of-concept code is already circulating in private security research circles.
- CISA emergency directive: The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is expected to issue an emergency directive requiring federal civilian agencies to patch all affected Linux systems within 48 hours, likely by May 3, 2026.
- Forensic tool updates: Security vendors such as CrowdStrike, SentinelOne, and Red Canary are updating their endpoint detection and response (EDR) agents to detect signs of Copy Fail exploitation, including abnormal page table modifications and unexpected file permission changes. These updates are expected within two weeks.
The Bigger Picture
The Copy Fail vulnerability underscores two major trends in cybersecurity. First, AI-Augmented Vulnerability Discovery is moving from theoretical promise to practical reality. KernelGuard AI's success in finding a high-severity, multi-year-old bug suggests that AI tools will increasingly become standard equipment for both defenders and attackers. Nation-state actors and advanced persistent threat (APT) groups are likely already deploying similar tools to find zero-day vulnerabilities at scale.
Second, the flaw highlights the growing risk of Kernel Complexity Debt. The Linux kernel now contains over 30 million lines of code, growing by approximately 2 million lines per year. Each new feature, driver, and architecture support adds surface area for race conditions and memory management bugs. The Copy Fail bug survived for five years despite extensive manual code review and fuzzing, suggesting that traditional security testing approaches are reaching their limits. The kernel community may need to adopt AI-assisted analysis as a standard part of the development workflow, rather than an occasional research tool.
Key Takeaways
- [Severity & Scope]: CVE-2026-31431 affects all major Linux distributions with kernels from version 5.10 onward, covering billions of devices worldwide.
- [Exploitation Ease]: The exploit requires only low-privilege shell access and leaves no log traces, making it a prime tool for lateral movement and persistence.
- [Patch Urgency]: Patches are available now; organizations should treat this as a 72-hour emergency patching event, not a routine update.
- [Broader Implications]: The AI-assisted discovery method signals a shift in vulnerability research that will accelerate both defensive and offensive capabilities.